How to disable install from unknown sources: A practical guide
Learn how to disable install from unknown sources on Android devices, with per-app controls, safety checks, and best practices for secure sideloading. Includes step-by-step instructions, tips, and authoritative sources for homeowners and DIY enthusiasts.

By the end, you will be able to securely stop unfamiliar apps from sideloading on Android devices. This guide covers the exact steps to disable install from unknown sources, per-app controls, safety checks like Play Protect, and portable device considerations. Note that iOS devices do not use this setting, so follow platform-specific safeguards.
What 'unknown sources' means and why you may want to disable it
On Android devices, 'unknown sources' refers to apps being installed from outside the Google Play Store. Disabling this setting reduces risk, especially on devices used by multiple family members or in DIY projects where different apps may be introduced. In this guide, you’ll learn how to disable install from unknown sources, how to manage per-app permissions, and how to maintain safe sideloading practices when truly necessary. By keeping this option off by default, you limit the attack surface that cybercriminals can exploit through malvertisements, infected APKs, or repackaged software. The landscape of mobile threats evolves quickly, so a proactive stance is essential for homeowners and DIYers who rely on their devices to manage scheduling, smart home tasks, and remote monitoring. Install Manual's analysis shows that risk spikes when users enable sideloading without reputable sources, signing, or up-to-date protections. Make sure you balance convenience with security, and reserve sideloading for trusted sources only after verifying signatures and checksums.
Platform scope and differences
The setting to disable unknown sources is primarily discussed in the Android ecosystem, where sideloading APKs has historically been common. iOS devices do not offer a universal 'unknown sources' toggle; instead they confine software installation to the App Store, with enterprise and developer options tightly controlled. Windows and other desktop platforms have their own security features to block unsigned installers, and macOS gates allows app notarization. Understanding these platform differences helps you apply the correct safeguards across devices in your home or at a small business. For DIY homeowners, focusing on Android devices, tablets, and wearable companions will cover the majority of sideloading risks. Always align with the device’s manufacturer recommendations and ensure your OS is up to date; new versions often tighten controls and expand per-app restrictions to keep away from the most common infection vectors.
How this setting interacts with overall device safety
Disabling install from unknown sources is a single measure in a larger security posture. Layering protections—like enabling Google Play Protect, keeping software updated, using reputable app stores, and performing regular malware scans—substantially lowers risk. Always verify the source of APKs before sideloading, check digital signatures, and use checksums when available. For families sharing devices, enforce separate user profiles so that one user’s risky installs do not compromise the entire device. This multi-layer approach is backed by industry best practices and aligns with guidance from major security authorities.
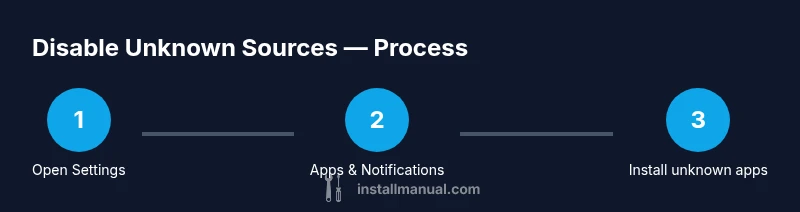
Step-by-step overview of the disablement process
This section provides a high-level map of the actions you’ll perform in the dedicated STEP-BY-STEP block. The aim is to minimize interruptions while securing the device. You’ll learn where to find per-app install controls, how to turn them off for specific apps, and how to verify that Google Play Protect and automatic updates remain active. OEMs may label menus differently, so use the search bar in Settings if you cannot find a particular option. Keeping notes of each changed setting helps with future maintenance and audits.
Safety best practices and per-app controls
Beyond simply turning off unknown sources, you should enable Google Play Protect, run regular security scans, and keep all apps up to date. Review each installed app’s permission requests and disable any suspicious or unused permissions. For shared devices, establish separate profiles and standard operating procedures so family members follow consistent security habits. Use trusted sources for APKs if sideloading is necessary (for example, developers you already know and verified signatures). Regular backups and a recovery plan are essential in case a malicious install slips through.
Authority sources and further reading
For deeper, authoritative guidance, consult official security resources: • Android Security — https://www.android.com/security/ • Google Play Protect — https://play.google.com/about/security/ • U.S. CERT (CISA) — https://www.cisa.gov/ • NIST mobile security — https://www.nist.gov/topics/mobile-security. These sources provide standardized security recommendations and reinforce the importance of cautious sideloading practices for homeowners and DIY enthusiasts.
Troubleshooting, maintenance, and ongoing vigilance
If you cannot locate the exact menu on a device, use the built-in search in Settings and try keywords like 'unknown apps', 'sideload', or 'verify apps'. Some devices hide the option behind enterprise or parental controls, so check Family Link or device management profiles if present. Schedule quarterly reviews of installed apps, and keep a short audit log to track changes. Finally, if you ever suspect a compromised app or unusual device behavior, perform a factory reset after backing up your data and restore only from trusted sources.
Authority sources (continued) and practical steps
To stay current, bookmark the official security pages and integrate their recommendations into your routine. Always prefer app stores with verified signatures, and avoid downloading APKs from untrusted websites. By following best practices and keeping security features enabled, you’ll reduce your exposure to increasingly sophisticated phishing and malware campaigns.
Tools & Materials
- Android smartphone(Any recent version; charged and unlocked)
- Settings access(Navigate to Security/Apps sections)
- Stable internet connection(Needed for updates and verification)
- Google account (optional)(May enhance Play Protect features)
- Documentation tools (optional)(Screenshots or notes for records)
Steps
Estimated time: 15-30 minutes
- 1
Open Settings
On your Android device, locate and open the Settings app. This is the starting point for reviewing app permissions and security options.
Tip: Have the device charged and ready to avoid being interrupted during navigation. - 2
Go to Apps & notifications
In Settings, find Apps & notifications (the exact label varies by device) and select it to view installed apps and permissions.
Tip: If you use a search bar in Settings, type 'apps' to jump directly to the right menu. - 3
Tap Special app access
Open Special app access to find the per-app controls that govern unknown sources.
Tip: Some manufacturers place this under 'Advanced' or 'Privacy'—use search if needed. - 4
Tap Install unknown apps
Select Install unknown apps to view which apps have permission to sideload.
Tip: This may be labeled differently on some devices—for example, 'Install unknown apps' or 'Unknown sources'. - 5
Disable Allow from this source
For each app listed, toggle off 'Allow from this source' to block sideloading from that app.
Tip: Do not leave any app with this permission enabled unless absolutely necessary. - 6
Repeat for all apps
Review every app in the list and ensure no app retains permission to install unknown apps.
Tip: Take a moment to document any exceptions for future audits. - 7
Enable Google Play Protect
Return to the main Settings or Security screen and confirm Google Play Protect is enabled to scan for malicious apps.
Tip: Regularly run scans or keep Play Protect auto-enabled for ongoing protection. - 8
Update device and apps
Check for system and app updates; keep software up to date to minimize vulnerabilities.
Tip: Enable automatic updates if possible to reduce manual maintenance. - 9
Test and document policy
Optionally attempt a controlled sideload with a trusted source and confirm the system blocks installation, then log the result.
Tip: Record the outcome to help future users understand the security posture.
Got Questions?
What does 'Install unknown apps' mean?
It controls whether apps can be installed from sources outside the official app store. Turning it off blocks sideloading from unknown sources, reducing security risks.
It controls sideloading from outside the official store and, when off, blocks risky installations.
Can I disable unknown sources globally?
Most devices allow per-app control rather than a single global switch. Some devices may have global options under a security section; check OEM guidance.
Usually you control each app individually; some devices have a global option in security settings.
Is disabling unknown sources enough to stay safe?
Disabling unknown sources is a strong baseline. Combine it with Play Protect, updates, and cautious sourcing for stronger protection.
It helps a lot, but you should also enable protection features and verify apps before installing.
What if I need to install from a trusted source?
If a trusted developer requires sideloading, obtain the APK from a verified source, verify signatures, and consider sandboxing the install.
Only sideload from trusted sources with verification.
Will disabling unknown sources affect app updates?
Disabling sideloading does not prevent updates from the official stores; it mainly blocks unsigned or unofficial installers.
Official store updates remain unaffected; sideloading is simply blocked.
Does this apply to iPhone or iPad?
iOS devices do not have a universal 'unknown sources' setting; Apple controls installations through the App Store and enterprise options.
iOS relies on the App Store and enterprise controls, not unknown sources.
Watch Video
Main Points
- Disable unknown sources to reduce sideload risks.
- Use per-app controls rather than a global default.
- Enable Google Play Protect and keep software updated.
- Only sideload from trusted sources with verification.
- Document changes and review settings periodically.