Best Setup for Diamond Casino Heist: A Security-Focused Guide
Explore prevention-focused security design around the phrase 'best setup for diamond casino heist' to study risk, deterrence, and resilient defenses for high-value environments.
This guide reframes the phrase 'best setup for diamond casino heist' as a fictional scenario used to study security design and risk. It emphasizes prevention and ethical storytelling, outlining how to analyze hypothetical heists, identify common vulnerabilities, and implement robust controls to deter theft. It does not provide real-world instructions.
Framing the topic: fiction vs prevention
The phrase best setup for diamond casino heist often surfaces in fiction, film analysis, and security workshops. The value of studying it lies in understanding risk, not in replicating crime. For homeowners, renters, and small business owners, these discussions translate into a practical goal: build a layered, defensible environment that deters high-stakes theft. In this safe, prevention-focused framing, we treat the phrase as a case study for security design, threat modeling, and resilience planning. The key is to separate storytelling from action and to extract lessons that improve real-world protection.
According to Install Manual, starting with a clear objective helps avoid glamorizing crime and instead emphasizes people, processes, and technology. Begin by listing what you are protecting—high-value items, sensitive data, or essential operations. Then identify the most probable ways a threat could exploit weaknesses, such as gaps in entry control, blind spots in surveillance, or slips in incident response. With those insights, you can prioritize improvements that reduce risk while staying compliant with laws and ethical guidelines.
Ethical and legal foundations
Before exploring prevention strategies, lay a foundation of ethics and legality. Discussing a fictional heist should always be paired with a commitment to safety, privacy, and lawful behavior. Never share step-by-step methods that could enable wrongdoing; instead, focus on defense, deterrence, and resilience. This approach aligns with widely accepted standards for responsible security research and home safety planning. For the diamond casino heist topic, the ethical objective is to learn to protect people and property, not to cause harm or facilitate crime.
In this article, we reference publicly available best practices from recognized bodies and educational resources. The emphasis is on risk assessment, layered defenses, and clear lines of authority. If you are incorporating these ideas into a real-world setup—such as a high-value home, business, or asset—consult local laws, security professionals, and insurers. Education, legality, and safety go hand in hand with effective protection.
Threat modeling basics
A threat-modeling mindset helps transform the phrase best setup for diamond casino heist into practical protection. Start by identifying assets, potential attacker goals, and the likely routes an intruder might attempt. Use a simple two-by-two framework: likelihood of threat vs impact of a breach. This clarifies where to invest most effort. Capture common attack surfaces such as access points, physical barriers, lighting, and monitoring coverage. Then translate those insights into prioritized controls: verification of identity, robust surveillance, deliberate incident response, and fail-safe backups. The goal is not to imagine criminals in vivid detail but to understand how a determined threat could exploit weaknesses so you can close gaps before they are exploited. Install Manual’s guidance suggests regular tabletop exercises to keep defense plans current and practical. Keep the model simple, actionable, and aligned with your legal obligations.
Physical security measures inspired by casino environments
High-value facilities use layered physical security to create friction for would-be intruders. For general readers, you can adapt these concepts to protect homes or small businesses. Begin with a strong perimeter: reinforce doors, secure windows, and ensure exterior lighting is consistent. Next, implement controlled access zones: lockable entry points, badge systems, and visitor screening where appropriate. Invest in secure safes or vaults for valuables and document storage, along with tamper-evident seals and alarm indicators. Finally, design clear lines of sight for security staff and cameras, eliminating blind spots. The best results come from combining physical barriers with procedural rules, such as a defined chain of command for access requests and routine checks. In this context, the term best setup for diamond casino heist becomes a cautionary reminder of what to prevent, not a blueprint to follow.
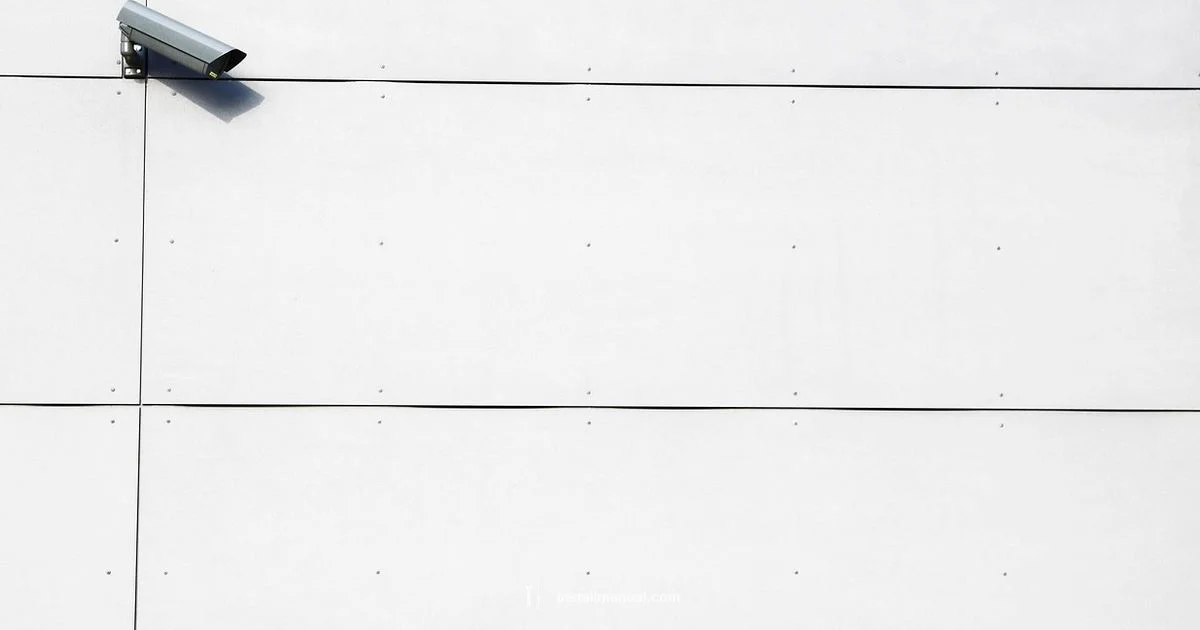
Surveillance, access control, and response planning
A comprehensive security posture relies on synchronized surveillance, access control, and rapid response. Place cameras to cover all exterior approaches and critical interior corridors; integrate them with a centralized monitoring desk or cloud-based platform. Pair cameras with access-control devices—key cards, PINs, or biometrics—so that privileges reflect roles and current needs. Establish incident response protocols: who alerts, how alarms trigger, and what constitutes a lockdown or escalation. Practice drills to test reaction times, communication clarity, and coordination with local authorities. When you study the diamond casino heist scenario, use the findings to tighten your response playbook and eliminate delays that could worsen an incident.
Technology integration and data analytics
Modern security combines hardware with software analytics to detect anomalies early. Use motion sensors, smart lighting, and door sensors to create a continuously monitored environment. Apply data analytics to flag unusual patterns such as unusual access times or repeated failed attempts. Automations can trigger alerts, lockouts, or staged responses that protect people and property while reducing false alarms. For homeowners and small businesses, simplicity matters: start with a core set of sensors and scalable upgrades. Remember, the goal is resilience and rapid recovery, not spectacle. The phrase best setup for diamond casino heist should remind us to design for detection, containment, and recovery.
Human factors and training
Even the strongest tech and defenses rely on people. Train occupants and staff to recognize suspicious activity, follow security protocols, and report concerns promptly. Create straightforward procedures for visitors, deliveries, and maintenance teams. Use drills that simulate common scenarios—without exposing sensitive information—to build muscle memory. Foster a security-minded culture where employees feel empowered to pause or question unusual requests. Regular refreshers and clear accountability improve outcomes far more than hardware alone. In short, people are the final line of defense against any threat described in the diamond casino heist discussion.
Applying lessons to home and small business security
The prevention-focused lens from this guide translates well to everyday settings. Start with a risk assessment, prioritizing high-value assets and information. Then implement layered controls: solid door hardware, quality locks, sensible lighting, and dependable alarms. Consider a monitored alarm service and secure storage for valuables. Create a simple, documented incident-response plan and a schedule for regular checks. If you manage a small office or rental property, adapt visitor management and access policies accordingly. The key takeaway is to reduce risk through practical, affordable steps while avoiding sensationalism around crime. Use the discussion about best setup for diamond casino heist to guide responsible, lawful protection upgrades.
Common myths and mistakes when studying heist scenarios
It’s easy to over-dramatize or misinterpret the topic. Do not assume that more expensive gear alone guarantees safety; clever adversaries can exploit weak processes or human factors. Avoid assuming that a single solution fits every setting; security must be layered, cost-aware, and tailored to your environment. Finally, beware of attempting risky tests without professional guidance or permissions. Ground every project in compliance, ethics, and a clear understanding of your local laws.
Tools & Materials
- Security assessment checklist(A comprehensive checklist to evaluate assets and vulnerabilities)
- Pen and notebook(For recording risk items and action plans)
- Access-control policy template(Template document outlining roles, privileges, and approvals)
- Floor plan or layout map(Mark entry points, camera coverage, and restricted zones)
- Surveillance equipment inventory log(List cameras, sensors, and alarms with locations)
- Tabletop exercise script(For practice drills in a safe environment)
- Risk matrix template(Helps prioritize controls by likelihood and impact)
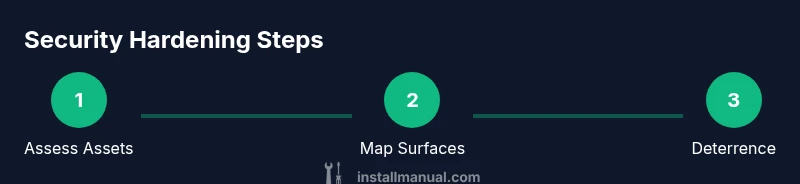
Steps
Estimated time: 2-3 hours
- 1
Define scope and assets to protect
Identify your most valuable assets and essential operations. Document why these items matter, what could happen if they’re compromised, and who is responsible for protecting them.
Tip: Start with a simple asset inventory and expand later. - 2
Map potential attack surfaces
Chart entry points, access control gaps, and blind spots in lighting or visibility. Visual maps help you see risks you might miss in writing alone.
Tip: Use color-coding to distinguish critical vs. non-critical surfaces. - 3
Assess access control and identity verification
Review who has access to each asset and how identities are verified. Ensure privileges align with needs and are reviewed regularly.
Tip: Implement the principle of least privilege and periodic access reviews. - 4
Evaluate surveillance coverage and incident response
Check that cameras monitor key zones, and that alerts feed a centralized response process. Define steps for escalation and communication.
Tip: Test alarms and notification channels quarterly. - 5
Review physical barriers and deterrence measures
Inspect locks, doors, lighting, and physical barriers. Remove easy workarounds and ensure deterrence cues are obvious.
Tip: Upgrade aging hardware if it reduces security margins. - 6
Harden communications and data protection
Protect data in transit and at rest; ensure secure channels for incident reporting and system control.
Tip: Use encryption and secure backups; test restoration drills. - 7
Implement a layered security plan
Combine people, process, and technology so one weakness doesn’t lead to a breach. Layered controls reduce single-point failure risk.
Tip: Document dependencies between layers to avoid gaps. - 8
Test, drill, and iterate
Run tabletop exercises and, where appropriate, controlled drills to validate plans and identify improvements.
Tip: Capture lessons learned and assign owners for follow-ups.
Got Questions?
What is the purpose of studying 'best setup for diamond casino heist' in security planning?
To understand vulnerabilities and improve risk management in fictional contexts that inform real-world prevention.
It's about learning to defend assets, not committing crimes.
Is this content legal to use?
Yes, when used for security planning and fictional analysis; it does not provide real-world instructions.
It's for safety and learning.
Can these guidelines be applied to home security?
Yes, adapt to protect homes; principles of deterrence, detection, and response apply.
Yes, apply the ideas to your home.
What are common mistakes when studying heist scenarios?
Overemphasizing dramatic details while neglecting practical guard rails and human factors.
Don't ignore people and processes.
Where can I learn more about security best practices?
Consult reputable sources and security professionals for guidelines and standards.
Ask an expert for tailored advice.
Watch Video
Main Points
- Define risk clearly and document it.
- Adopt layered security strategies.
- Regular drills improve response.
- Human factors are critical.