What to Do When You Install Linux: A Practical Post-Install Guide
Learn essential steps after installing Linux, from updates and security to drivers and backups. This guide walks homeowners and DIY enthusiasts through the post-install setup for a stable, secure system.

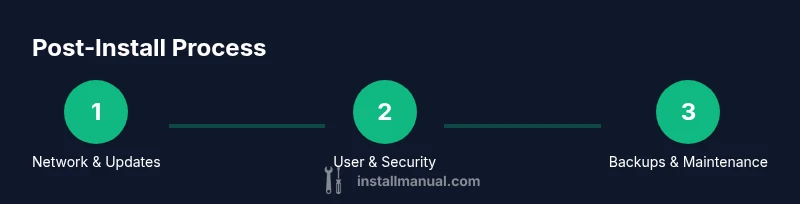
After you install Linux, you’ll want to secure, update, and tailor the system for daily use. This quick answer highlights the essential post-install steps: verify internet access, update the package manager, install essential software, configure users and permissions, enable backups, and set up basic system preferences. Following these steps ensures a stable, secure, and comfortable environment for long-term reliability.
what to do when you install linux
Immediately after installation, verify basic network access and confirm you can reach the package repositories. This ensures subsequent updates and software installs succeed. According to Install Manual, the next step is to create a non-root administrator account and configure sudo privileges so daily tasks don’t require logging in as root. Finally, establish a simple backup plan to protect your data from the start. Consider enabling a basic firewall and reviewing default services to minimize exposure. This approach reduces risk and sets a reliable tone for the rest of the setup. Time your initial checks to avoid surprises later, and document your initial configuration so you can reproduce it on future machines. If you’re on a laptop, test suspend/resume behavior and screen locking to ensure power management works smoothly.
Security foundations for a Linux install
Security begins at the moment you complete the installation. Start with a baseline firewall configuration, even if you’re not exposed to the internet directly. Ensure you have a non-root user with sudo privileges and a strong, unique password, or, preferably, an SSH key-based login if you enable remote access. Regularly review services that start on boot and disable any that aren’t needed. While some distributions ship with minimal defaults, taking ownership of these settings reduces the attack surface from day one. Remember to rotate credentials periodically and keep a simple, written checklist for future audits. This section aligns with best practices recommended by the Install Manual team and is essential for long-term security.
Update management and software selection
Post-install software management is a core habit. Begin with updating the package lists and upgrading installed packages so you’re running supported software with the latest security patches. Choose essential tools that match your workflow—text editor, file manager, media codecs, and developer tools as needed. The Install Manual analysis shows that systems with current updates experience fewer crashes and security incidents. Prefer official repositories first, then consider reputable third-party sources if you need specialized software. Always verify signatures or checksums when retrieving packages and avoid mixing too many sources at once.
Drivers, hardware, and peripherals
Hardware compatibility is a frequent source of post-install headaches. Start by checking for available drivers for your graphics card, chipset, and wireless devices. Many distributions offer an easy in-system utility to install closed-source drivers if necessary, while most audio devices work fine with open-source drivers. If you rely on a printer, scanner, or other peripherals, install the corresponding drivers or software packages. Keep notes about hardware quirks (for example, wifi intermittency or printer queue delays) so you can troubleshoot quickly later. A methodical approach minimizes frustration and helps you avoid driver conflicts.
Data safety: backups and recovery planning
Backups are your safety net. Configure a regular backup strategy that protects important data and configuration files. Use local backups to an external drive or network share, and consider cloud-based solutions for off-site redundancy. For system-level recoveries, create a snapshot or system image when possible, and test the restore process occasionally to ensure you can recover quickly after a failure. Keep a documented backup schedule and verify the integrity of backups periodically. A consistent backup routine dramatically reduces downtime after hardware failures or user errors.
Customization and productivity: tailoring Linux to your workflow
The post-install phase is the right time to tailor your environment to your daily tasks. Install your preferred desktop environment or window manager, adjust fonts and themes for readability, and set up keyboard shortcuts that mimic your prior OS if you’re transitioning from Windows or macOS. Create a set of shell aliases or small scripts to automate repetitive tasks, and organize your home directory with clear conventions for documents, media, and projects. Keep your dotfiles under version control so you can reproduce your environment on new machines. A well-organized workspace boosts productivity and reduces cognitive load.
Performance tuning and system hygiene
Performance gains come from deliberate management of resources and services. Review which daemons start at boot and disable those you don’t need. Optimize swap usage and select an appropriate I/O scheduler if your drive type justifies it. Regularly clear package caches and rotate log files to prevent disk bloat. Invest time in learning your distro’s monitoring tools to identify bottlenecks, such as high CPU usage, memory pressure, or disk I/O waits. A clean, well-tuned system remains responsive and reliable under heavier workloads.
Remote access, SSH hardening, and access controls
If you need remote access, configure SSH securely. Use key-based authentication, disable password login, and limit which users may connect. Change the default SSH port only if you know you’ll manage the risk of non-standard ports. Consider setting up two-factor authentication for critical systems and enabling fail2ban or similar protection to deter brute-force attempts. Remote management should be deliberate, auditable, and restricted to trusted networks. These steps protect your machine without hindering legitimate remote work.
Troubleshooting and quick fixes: building your fall-back kit
Even a well-planned setup encounters issues. Common post-install problems include network not starting, display manager not launching, or missing drivers after a kernel update. Build a small fall-back kit: a live USB for repair, a short list of commands you’ve tested, and a plan to revert updates if something breaks. Log files in /var/log, journalctl, and dmesg are your first friends when diagnosing boot or hardware problems. Keep a calm, methodical approach: reproduce the problem, capture error messages, search for official guidance, and apply targeted fixes one at a time.
Final checks before you go productive
Before you consider the system ready for daily use, verify your backup strategy, validate your network, and confirm you can restore from a backup. Run a quick sanity check of essential services such as your package manager, firewall status, and SSH access (if enabled). Ensure time synchronization is accurate so logs and authentication events line up with real-world events. Finally, document your configuration decisions so you can scale this setup to future machines or share your approach with others. A disciplined finish makes the long-term experience smoother.
Tools & Materials
- Computer with internet access(Needed to download updates and packages during setup)
- Linux distribution installer media(USB/DVD or network install method; bootable medium)
- Admin user account(Non-root user with sudo privileges)
- Backup medium(External drive or cloud backup for initial data safety)
- Firewall utility(Optional; many distros include firewall by default)
- USB drive for live troubleshooting(Helpful if testing live environment)
- Secure shell client(Use if enabling SSH for remote access)
Steps
Estimated time: 120-180 minutes
- 1
Verify internet connectivity
Ping a reliable host and ensure DNS resolution works. This confirms the system can reach the repositories needed for updates and software installation.
Tip: If the network is behind a proxy, configure it now to prevent later failures. - 2
Update package lists and upgrade
Refresh package indices and apply upgrades so you run supported software with current security patches. This avoids compatibility issues after installation.
Tip: Use the recommended commands for your distro and verify success with a short check of the package manager’s status. - 3
Create a non-root sudo user
Add a normal user and grant sudo privileges. This reduces the risk from daily tasks performed as root and aligns with best practices.
Tip: Choose a strong, unique password or configure SSH keys for remote admin access. - 4
Set strong passwords and password aging
Enforce long, complex passwords and enable aging to prompt changes periodically. This improves long-term account security.
Tip: Avoid reusing passwords across services. - 5
Configure automatic security updates
Enable unattended upgrades or automatic security updates where available. This helps protect the system from known vulnerabilities.
Tip: Review upgrade logs occasionally to catch issues early. - 6
Install essential utilities
Add utilities for file management, networking, text editing, and media playback that fit your workflow. Keep the set lean to avoid bloat.
Tip: Prefer official repositories to keep upgrades reliable. - 7
Configure backups
Establish a backup routine for personal data and critical configurations. Use local and off-site options where possible.
Tip: Test restoration from backups periodically. - 8
Enable and configure a firewall
Turn on a basic firewall and define rules that block unnecessary inbound connections while allowing essential services.
Tip: Document the rule changes so you can adjust them later if needed. - 9
Secure SSH if remote access is needed
If you’ll access the machine remotely, set up SSH with key-based authentication, disable password login, and consider limiting user access.
Tip: Place your SSH key on a secure device and back up the private key in a safe location. - 10
Install driver packages for hardware
Check for hardware requiring drivers (graphics, wifi, sound) and install those recommended by your distro.
Tip: Test hardware components (wifi, sound, display) after installation to confirm functionality. - 11
Tune startup services
Review services that run at boot and disable unnecessary ones to improve boot time and resource use.
Tip: Document changes so you can revert if needed. - 12
Perform a post-install health check
Run a quick audit of disk space, memory usage, running processes, and essential system health indicators.
Tip: Create a short checklist you can reuse after future installs. - 13
Finalize baseline documentation
Record usernames, commands, installed software, and configuration decisions to facilitate future maintenance.
Tip: Store notes in a version-controlled dotfiles repository if possible.
Got Questions?
What should I install first after a fresh Linux install?
After installation, update the system, set up a non-root user with sudo, enable a firewall, and configure basic backups. These steps establish a secure and reliable baseline for further setup.
First, update and secure the system, then add a non-root user and set up backups.
Do I need to enable a firewall on Linux?
Yes. A basic firewall helps block unwanted inbound connections and reduces exposure. Most distributions include firewall utilities you can enable with minimal configuration.
Yes—enable a firewall and configure sensible rules.
How should I back up Linux system data?
Plan a backup strategy using local and remote options. Use tools like rsync or snapshot-based solutions and regularly verify that you can restore data.
Set up backups and test restores regularly.
Should I enable SSH by default?
Only enable SSH if you need remote access. Use key-based authentication, disable password login, and restrict access to trusted networks.
Only enable SSH if you truly need remote access, and secure it properly.
What about drivers for hardware?
Check for recommended drivers for your hardware and install them. Start with open-source options; install proprietary drivers only if necessary for performance or compatibility.
Install drivers only if you need them for hardware performance.
How can I keep this system secure over time?
Keep the system updated, monitor logs for unusual activity, and periodically review user permissions and installed services.
Keep updates current and monitor your system regularly.
Is it worth using unattended upgrades?
Unattended upgrades can improve security, but review what gets installed and monitor for stability after updates.
Unattended updates help security; check stability after updates.
What should I do if a kernel update breaks things?
Keep a fallback plan: be prepared to boot into an earlier kernel from the boot menu and note any hardware-related issues to troubleshoot.
If a kernel breaks things, revert to an earlier version and investigate.
Watch Video
Main Points
- Start with a secure, updated baseline
- Create a non-root admin user and practice least-privilege
- Back up data and test restores regularly
- Document your configuration for future systems
- Fine-tune performance and startup services over time